
experience
Security for your AWS infrastructure
Empower your startup’s growth with cutting-edge AWS security services that ensure your cloud infrastructure is protected from threats and vulnerabilities.
Experience
We provide you with top notch services for your project success.
Prompt Support
We've got your back from every angle.
Secure Every Aspect of Your Organization
-
Application Security Posture Management
Application Security Posture Management ASPM operates at the application layer, overseeing applications in both on-premises and cloud-based environments to detect and address potential security risks associated with these applications. ASPM focuses on managing the security posture of applications throughout their lifecycle. ASPM is gaining importance due to several factors: Applications are becoming significantly more complex, especially […]
-
Cloud Security Posture Management
Cloud Security Posture Management What is cloud security posture management (CSPM)? Cloud security posture management (CSPM) identifies and mitigates risk by automating visibility, continuous monitoring, threat detection, and remediation workflows to look for misconfigurations across various cloud environments/infrastructure, including: Infrastructure as a Service (IaaS) Software as a Service (SaaS) Platform as a Service (PaaS) CSPM […]
-
Cloud Network Security
Cloud Network Security Cloud network security is vital because organizations adopt different approaches, controls, and procedures to secure application data. With cloud network security, you can protect your users, get answers to everything on the cloud these days, and get the required support. Good cloud network security can help you continue your business operations and […]
-
Threat Intelligence & Management
Threat Intelligence & Management Don’t just detect threats, act on them. We help you to spot attacks early, respond effectively, and keep the business running with confidence. Expert-led detection and response for threats Leveraging a detection and response services tackle incidents at every stage – monitoring throughout the threat lifecycle to ensure rapid containment, minimal […]
-
Cloud Security
Overview Cloud security solutions are software tools that secure cloud architectures and identities, identify and remediate vulnerabilities, prevent threats, and help respond to incidents when they occur. Data privacy and security concerns continue to grow as more and more businesses adopt cloud infrastructure, and use cloud resources to store sensitive data and run mission-critical applications. […]
-
Code Security
Code Security Overview For development, operations, and security teams overwhelmed by a growing backlog of reported security vulnerabilities, Code Security solutions deliver runtime-based prioritization of vulnerabilities with a platform approach to remediation. A unified, end-to-end solutions allow teams to focus on fixing vulnerabilities that matter, with clear visibility into remediation progress across the software development […]
-
DevSecOps
DevSecOps Assessment Our team of cloud-native security specialists can share DevSecOps best practices and compliance assessments across your cloud infrastructure and processes. DevSecOps assessment is carried out by our cloud-native security experts on your complete stack including nodes, applications, CI/CD pipelines, and cloud infrastructure. We have experience in securing bare-metal Kubernetes, Managed Kubernetes services like […]
-
Security Orchestration Automation & Response
Security Orchestration Automation and Response – SOAR As cloud environments grow more complex, security teams face challenges such as alert overload and manual, fragmented triage processes that strain resources and slow response times. Accelerate Incident Response Automate detection and response to reduce risk and speed up resolution. Break down silos Streamline collaboration and improve operational […]

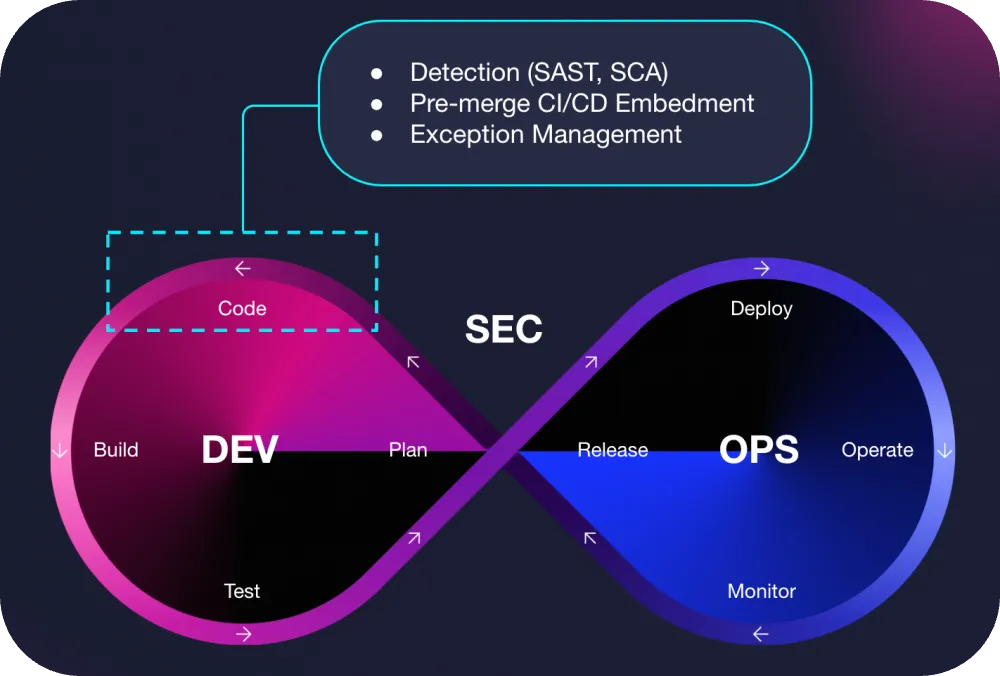
Our DevSecOps in 3 easy steps
Planning Your Story
We start by understanding your architecture, risk profile, and release goals. Security isn’t a checklist, it needs context to work.
Developing Solutions
Our experts integrate secure coding practices, secrets management, and static testing directly into your workflows. No more late-stage rewrites.
Testing and QA
The team combines SAST, IAST, DAST, and manual testing to uncover vulnerabilities that slip through automation before they reach production.
Our Customer Stories
Don't just take our word for it
Xandr
Autodesk
Paypal
Equip health
Promosis
Latest Blogs and Insights
Top 10 Cloud Security Challenges in 2025
Implementing Shift-Left Strategies for AWS Native CI/CD Pipelines
Amazon GuardDuty ECS runtime monitoring with Fargate
DAST – Automating Web Application Security Scans Using OWASP ZAP in AWS CodeBuild
Shift security left and stay ahead of threats.
Speak with us today to explore how XantraTech can help development teams build more secure software from the start.
General enquiries
info@xantratech.com
Customer sales enquiries
United States
+(760) 514-4035
Morocco
+(212) 6-62-63-81-14
Got an App in Mind?
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.